Twitter was in the news last year when accounts of celebrities got hacked, and their accounts were taken over. Scammers targeted nearly 130 Twitter accounts of well-known personalities, including Jeff Bezos, Bill Gates, Elon Musk, Barack Obama, and corporate accounts of Apple, Uber, and many others. You could be next! How do you know if your Twitter account is hacked? What should you do if your account gets hacked? And how do you secure your Twitter account? Read along to know the tell-tale signs of a hacked Twitter account and ways to recover it.
By Rudra Srinivas, Senior Feature Writer, CISO MAG
How to check if your Twitter account has been hacked
These are signs that your account has been compromised:
- A change in your name, profile picture, or email address
- New friends or friend requests from strangers with dubious handles
- Unauthorized or inappropriate tweets you did not post
- Following or unfollowing Twitter accounts
- Your password is no longer working, and you are being prompted to reset it
How to recover a hacked Twitter account?
You must act immediately as soon as you become aware that your Twitter account is compromised. It leads to a breach of critical information if a threat actor has access to your personal information for a long time.
Step 1: Reset Your Password
If your account is compromised but you’re still able to log in, change your account password immediately.
To change your password, click on the More option on the homepage >> select Settings and Privacy >> finally click on Change Your Password.
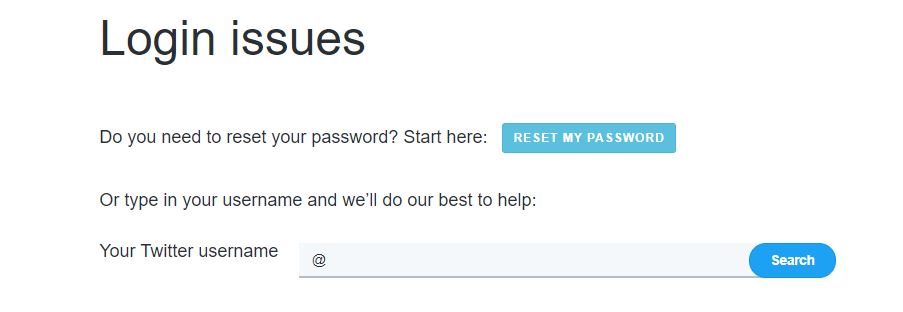
Step 2: Account Recovery
If you are unable to access your account, you’ll have to recover it.
For the Twitter account recovery system, click on Forgot Password on the login page >> enter your email, phone number, or username and click Search >> select the account recovery method >> provide the required details and follow the instructions >> after verifying your account click Reset Password to complete the account recovery process.
Step 3: Report the Hack
If you’re still unable to regain access to your compromised account, you should report directly to Twitter Support and select Hacked Account option. The support page displays options to recover your compromised account.
How to avoid getting hacked again?
- Use strong passwords that are a mix of upper and lower case and numbers (e.g. LearnttoRIDEabikeat5)
- Enable Twitter’s two-step authentication (use an Authentication app)
- Cross-check the URL for spelling discrepancies before logging in
- Avoid public Wi-Fi
- Beware of third-party apps’ permissions
- Avoid social logins
Conclusion
Social media accounts have growing importance because people share their personal experiences on virtual communities. With attackers leveraging innovative tactics to exploit loopholes on social media platforms, it is imperative for users to step-up their social media network security. Your social media handles will be secure only when you follow proper security measures.
The Twitter hack is an example of the fact that a human is the weakest link in cybersecurity. According to a Black Hat survey, “A single human mistake, can result in an attacker taking over all of the organization’s infrastructure, no matter what hardware, software, or endpoint security implementation has been done from the defensive team.”
Adhere to Twitter’s new security and privacy policy and observe your account’s activities closely to ensure there are no suspicious activities.
About the Author
Rudra Srinivas is a Feature Writer and part of the editorial team at CISO MAG. He writes news and feature stories on cybersecurity trends.